Could You Spot a Phishing Email? A Quick Guide for Everyday Staff
Phishing emails used to be easy to spot. Bad spelling, dodgy logos, a Nigerian prince needing your help moving $4…
Helpful Blogs written by the staff at Key IT
Phishing emails used to be easy to spot. Bad spelling, dodgy logos, a Nigerian prince needing your help moving $4…
Most people use about 10% of what Microsoft 365 can do. That’s not a criticism — there’s just so much…
If you run a small or medium business, you’ve probably had at least one of the following thoughts in the…
If you run a business in Melbourne’s northern suburbs — Greensborough, Eltham, Diamond Creek, Bundoora, Heidelberg, Watsonia, or anywhere along…

You’ve probably heard your IT team or boss mention “the Essential 8” lately. Maybe it came up in a meeting,…
At some point, your boss or IT team probably mentioned the company is “moving to the cloud” or already has….
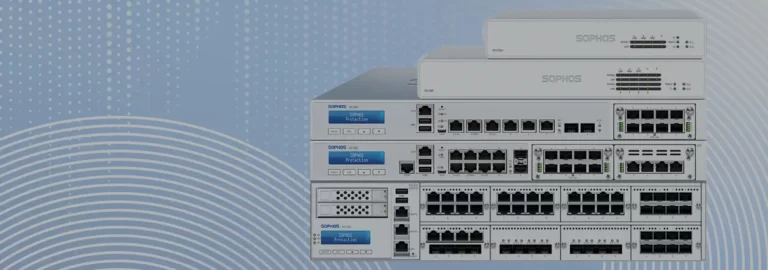
The Significance of a Corporate Firewall in Protecting Businesses from Cybercrime Discover the crucial role of a corporate firewall in…

Cybersecurity threats are on the rise, and businesses are under constant attack. As a business owner, it’s crucial to take…

Learn why data backup and disaster recovery planning is crucial for your business’s continuity and resilience. Our IT support blog…

Cloud computing has become an increasingly popular option for businesses in recent years. It offers several advantages over traditional on-premises…